How to Mitigate Terrapin Vulnerability through Registry Parameter in IGEL OS
To mitigate Terrapin Vulnerability, you can enable a registry parameter that will disable weak MACs and Chipers to prevent terrapin attacks. For more information on terrapin attacks and the related CVE-2023-48795, see Security & Safety > IGEL Product Security Information > ISN 2023-39: SSH Terrapin Vulnerability and https://terrapin-attack.com/ and https://cve.mitre.org/cgi-bin/cvename.cgi?name=2023-48795.
If you use OpenSSH 9.6p1 both on the client and server there is no need to use this registry parameter. IGEL OS versions 12.3.1 or higher use the latest OpenSSH 9.6p1. When you use this version or newer on the peer, they will automatically use the new "strict KEX" protocol extension.
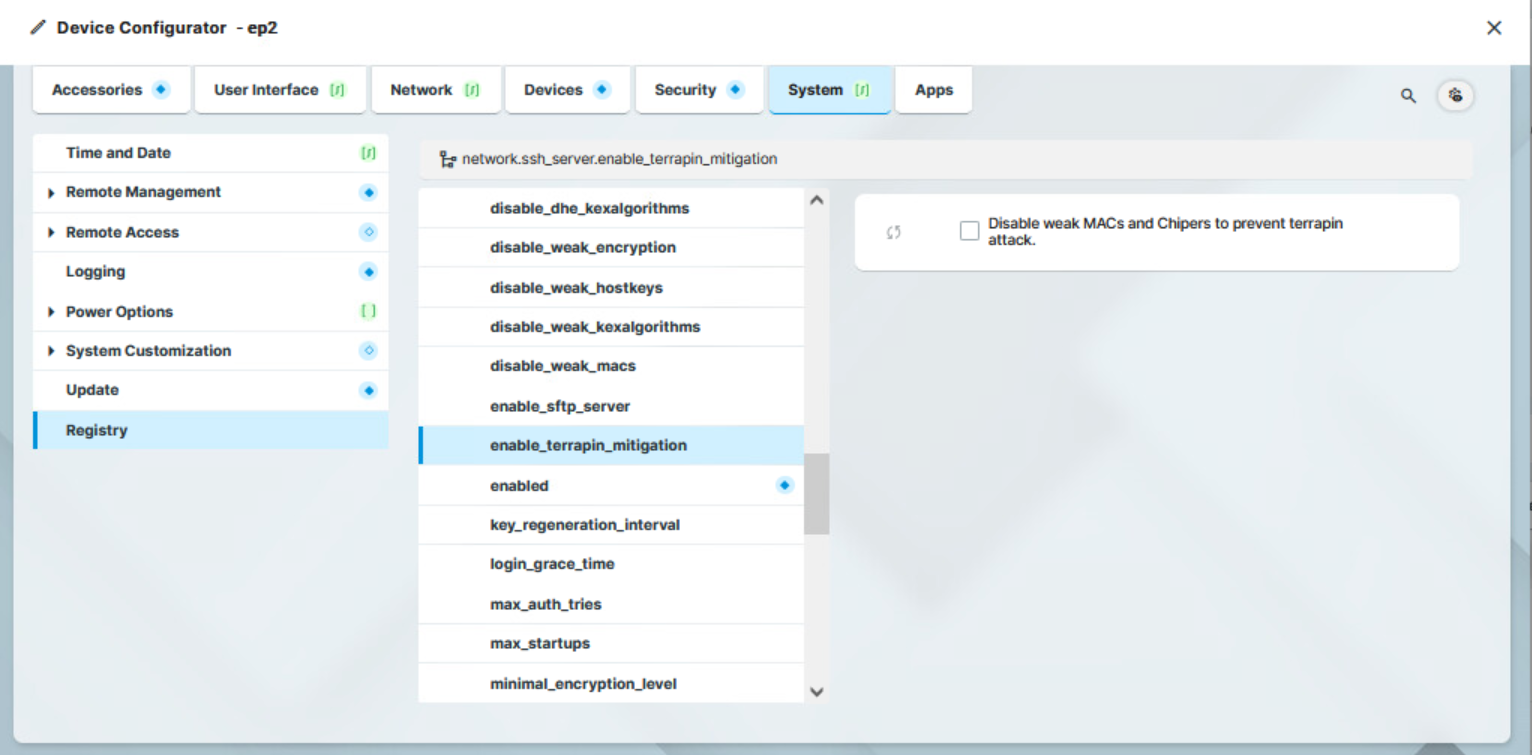
To enable Terrapin mitigation through the registry parameter:
In configuration, go to System > Registry > network > ssh_server > enable_terrapin_mitigation.
Enable the parameter.
Click Save or Save and Close to save the change.
The following options vulnerable to Terrapin attack are disabled:
the ChaCha20-Poly1305 cipher
all -cbc ciphers
all -ctr ciphers
all -etm@openssh.com macs
