Smartcard Authentication in IGEL OS
The following article provides an overview of how you can configure smartcard authentication in IGEL OS for various sessions like RDP, VMware Horizon, etc. as well as explains how you can set up Active Directory login with a smartcard and local login with a smartcard certificate.
If you use IGEL smartcards, see also Authentication with IGEL Smartcard.
Certificate Authentication
The smartcards discussed here can hold digital certificates (x.509) and corresponding private keys. The private key cannot be read from the card, but it can be used by the card itself for signing and decryption of data.
This enables the use of what is known as two-factor authentication: the user not only possesses the smartcard, he or she can also prove the knowledge of the smartcard PIN by signing data using the private key stored on the smartcard.
If you want to use Active Directory (AD), the certificate chain used by the key distribution center (domain controller) must be available on the device. To deploy certificate files, register them in the UMS (set Classification to "SSL Certificate") and assign to the devices, see Universal Management Suite > UMS Reference Manual > Files - Registering Files on the IGEL UMS Server and Transferring Them to Devices.
Smartcard Readers
Smartcards are accessed via smartcard readers, using either a contact or contactless interface. The IGEL Third Party Database lists the readers supported in IGEL OS.
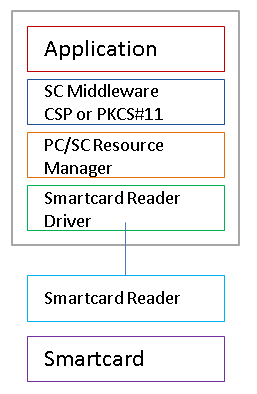
PC/SC Resource Manager
The PC/SC Resource Manager is a common Application Programming Interface (API) that is available on Windows and Linux operating systems. It provides a standardized way for applications to handle smartcards and readers.
The PC/SC Resource Manager is active by default in IGEL OS and can be controlled in the IGEL Setup via the Activate PC/SC daemon parameter under Security > Smartcard > Services.
Smartcard Middleware
In order to provide a generalized interface to different types of smartcard hardware, there is an additional software layer called smartcard middleware.
There are different types of middleware:
Windows | Linux | |
CSP, Cryptographic Service Provider | ✓ | |
PKCS#11, Public-Key Cryptographic Standards | ✓ | ✓ |
Some of the smartcard authentication methods require smartcard middleware to be installed on the endpoint device. The following modules are available:
Gemalto SafeNet
cryptovision sc/interface
Gemalto IDPrime
Athena IDProtect
A.E.T. SafeSign
SecMaker Net iD Enterprise (formerly called "SecMaker Net iD")
SecMaker Net iD Client (the next generation of SecMaker Net iD Enterprise, see http://docs.secmaker.com/net-id-client/latest/index.html)
Coolkey
OpenSC
90meter
Licensed Feature
This feature requires an add-on license; see IGEL Subscription and More > Hide from Viewport IGEL Software License Overview > Add-On Licenses. Please contact your IGEL reseller.
For information on how to use a custom PKCS#11 library, refer to the article Using a Custom PKCS#11 Library.
